Computers & Writing 2015 Town Hall
Question and Answer session with the Audience

When we first put together our pitch for the Computers & Writing Town Hall on privacy, surveillance, and net neutrality, we knew we wanted to have as much audience interaction as possible. Our proposal stated that we would have three main goals for the presentation:
- (21–35 mins): Introduction to the interactive town hall from seven facilitators, with a range of experiences from established scholars, mid-career researchers, and newcomers, with brief 3–5 minute roundtable remarks for some framing and research on the issues.
- (35–45 mins): Interactive town hall with the goal of community engagement and conversation that we envision as laying the groundwork for position statements for the Conference on College Composition and Communication's (CCCC) Committee on Computers in Composition and Communication (7Cs) to present to the CCCC Executive Committee. One speaker will record audience comments via Google docs and share the link with interested audience members at the conclusion of the town hall.
- (5–10 mins): Final remarks will call on pathways to action, generated by the community in the interactive town hall and recorded for future collaboration.
After a lively set of presentations from each of the presenters—Estee Beck, Angela Crow, Jennifer deWinter, Laura Gonzales, Heidi McKee, Colleen A. Reilly, and Stephanie Vie—we moved into a question and answer session with the audience. The entire Town Hall was recorded and the audience was made aware of this recording and encouraged to share their information with the panel to recieve a copy of the recording. Here we attempt to capture the general tenor of this question-and-answer session and include audio clips from the presenters' responses. (Because of the recording technology—a laptop with Audacity installed—most of the audience members' questions are very quiet on the recording, so in lieu of providing the recordings, we have typed out the questions.) During the session, Twitter was used as well to respond to the Town Hall presentations as well as illustrate some of the audience members' responses and questions; we have included selected tweets here that we think highlight some of the main elements of the conversation.
Taking Action
We are becoming hyper-aware of how much we're being tracked and what's actually happening with interactions and how much we can choose to ignore. But I constantly question what can we actually do about it other than analyze what's happening or choose how much to interact with these apps, other than develop our own apps that maybe don't participate in this kind of tracking. What do you all think about the degree to which we have control over this kind of tracking and what we can do to alter these methods?—Rachel Chapman
Stephanie saw this as an opportunity to promote some of the really interesting work she knew that Estee had done with gaming Facebook's algorithms and then leaving the site completely. You can hear Estee talk about her experiments here.
Transcript (pdf)She also recommends donating to groups like the Electronic Frontier Foundation and supporting their work monetarily.
Jennifer follows up with examples drawn from everyday life that illustrate how we are often willing to give up some of our data in exchange for small rewards—like receiving a $1.50 coupon for using a shopper's card which allows the supermarket to track our shopping habits. Listen to her discussion here.
Transcript (pdf)
Is it about teaching consequences? Because I think that all of my students know they're tracked all the time. And they all sign yes on the privacy waivers and stuff like that, but they want the cookie. So is there a way that we not only raise awareness but make really explicit what the cost is? ... I'm just wondering if there's a step further where we can show what it can cost besides just considering it...—Jen Almjeld
Stephanie discussed the difference between thinking about privacy in theoretical terms versus actually seeing what happens after deliberate, specific interactions with technological systems. This can help overcome the third-person effect, where individuals may believe that media will impact others but not them. Listen to Stephanie's discussion here.
Transcript (pdf)
Colleen followed by describing how teachers can design projects that show students what's actually happening when they run a search: By running repeated searches with different information each time, they begin to see how a site like Google presents them with different results based on the data they are providing to the system. You can hear Colleen's description of her assignment here.
Transcript (pdf)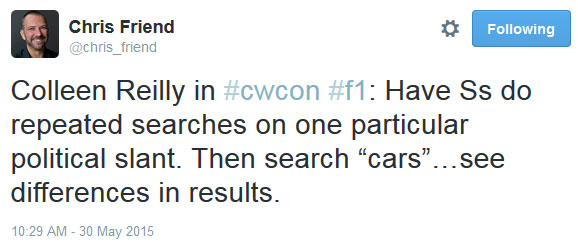
Resources and Future Research for the Field
Angela Crow underscored how we (especially in first-year writing) have access to an "extraordinary data pool that is tapped often, continually, by [Pearson's] MyCompLab, by Bedford, by people in the field" who have to navigate hundreds or thousands of sections of composition. That data needs to be in the hands of people like us, and we need access to that data. Instead, they sell that data back to us.
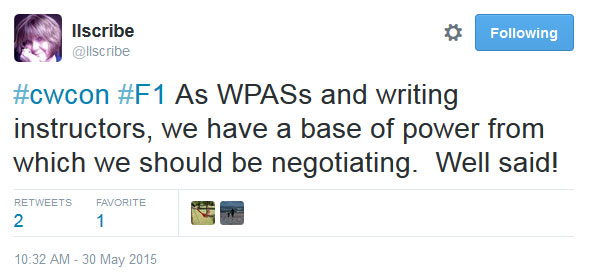
Can we acknowledge our uncomfortable reciprocity in this process? ... Can we design assignments that still teach digital literacy and rhetorical engagement while finding tools as instructors that aren't going to be tracking them in ways that we know are as harmful?—Jenae Cohn
I was going to ask a very similar type of question because as a faculty member who uses social media in my classes, I feel at once complicit with and resistant to these privacy and surveillance issues and the responsibilities I have to my students. ... I think we need policy statements about social media use in our classroom, a rationale for why we use them, an understanding of how we use them, and in my own case, I've thought about the ways I can allow students to opt out.—Kris Blair
The conversation ebbed and flowed with exciting ideas for future research in the field, from policy statements to the need for faculty training materials, particularly at small teaching colleges. And while audience members and panelists alike both hopefully left with feelings of accomplishment at the conversations that emerge, we hope to see these conversations continue. Not only is this webtext for the 20th anniversary of Kairos one small step toward continuing those conversations, we see opportunities for future discussions that can move us forward in meaningful ways. If you were at the Computers & Writing 2015 Town Hall on privacy and surveillance and want to be involved—or even if you're reading this webtext now and you want to be involved—please reach out to one of the Town Hall members. You can use the Twitter, Facebook, or mailto links at the bottom of the page or send a tweet to Estee or Stephanie, and we'll be happy to help.